You check your phone. A message pops up from what looks like your favorite exchange. It says your account is locked unless you verify your details immediately. You click the link, type in your password, and maybe even your recovery phrase. Within seconds, your wallet is empty. The money is gone, and because of how blockchain works, there is no customer service number to call for a refund.
This isn't a hypothetical nightmare. It’s the daily reality for thousands of people navigating the world of digital assets. Cryptocurrency phishing scams have evolved from clumsy emails into sophisticated psychological traps that exploit trust, fear, and curiosity. Attackers don’t just want your data; they want your private keys, which are the only thing standing between you and your funds.
The Anatomy of a Crypto Phish
To understand how to stop these scams, you first need to understand how they work. Unlike traditional banking fraud, where a bank can reverse a transaction, cryptocurrency transactions are irreversible. Once you send tokens to a scammer’s address, they are gone forever. This creates a high-stakes environment where attackers use every trick in the book.
The core goal is always the same: stealing your credentials. But the methods vary wildly. Some attacks rely on simple mistakes, like clicking a bad link. Others require weeks of building a fake relationship with you. Let’s break down the most dangerous types you’ll encounter in 2026.
Targeted Attacks: Spear Phishing and Whaling
Generic spam emails are annoying, but they are rarely effective. The real danger comes from targeted attacks. Spear phishing is when an attacker researches you specifically before striking. They might look at your LinkedIn profile, see that you work for a tech company, and send an email that appears to come from your IT department asking you to update your security settings. Because it’s personalized, it bypasses your natural skepticism.
An even more extreme version is called Whaling. This targets high-profile individuals, like CEOs or famous investors. If a CEO clicks a malicious link, attackers might gain access to the entire company’s network, including corporate treasury wallets. These attacks involve deep reconnaissance and often mimic urgent business requests to trigger a quick, unthinking response.
- Spear Phishing: Personalized emails targeting specific individuals based on known information.
- Whaling: High-level spear phishing targeting executives or public figures.
Technical Tricks: Clone Phishing and Pharming
Sometimes, the attack doesn’t look new at all. Clone phishing involves attackers taking an email you’ve already received from a legitimate source-like a newsletter from Coinbase-and creating an exact copy. They replace the original links with malicious ones. Since you’ve clicked this email before, your brain treats it as safe, leading to habitual clicking without checking the URL.
Then there’s Pharming. This is scarier because it happens even if you type the correct website address. Attackers infect DNS servers (the system that translates website names to IP addresses) with malicious code. When you type "binance.com," you might actually be directed to a fake site that looks identical but captures your login details. You did nothing wrong, yet you’re still compromised.

The Human Element: Romance and AI Scams
Not all scams happen via email. Some happen through conversation. Pig butchering schemes start as innocent chats on dating apps or social media. The scammer spends weeks building emotional trust, pretending to be a successful investor. Slowly, they introduce you to a "guaranteed" crypto investment platform. By the time you invest significant money, the platform locks you out, and your new friend disappears.
In 2026, this threat has been amplified by AI-powered impersonation. Scammers use deepfake technology to create videos of celebrities or influencers promoting fake giveaways. You might see a video of Elon Musk offering free Bitcoin if you deposit a small amount first. The voice, face, and mannerisms are perfect, but the person is entirely fabricated. Always remember: no celebrity will ever DM you to give away free crypto.
| Scam Type | Method | Primary Goal |
|---|---|---|
| Spear Phishing | Personalized emails using victim's info | Steal credentials or install malware |
| Pig Butchering | Long-term romance/investment buildup | Drain large investments on fake platforms |
| Pharming | DNS redirection to fake sites | Capture login data silently |
| Wallet Draining | Malicious smart contract approvals | Auto-transfer all tokens |
Wallet Security: The Silent Threats
Your wallet is your bank. Protecting it requires more than just a strong password. One of the most devastating modern threats is Smart contract approval scams. You visit a website to mint an NFT or play a game. It asks you to "approve" a connection. You click approve, thinking it’s just a one-time fee. In reality, you’ve granted that contract unlimited access to your wallet. The scammer then drains every token you own instantly.
Another common trap is the Fake Airdrop. You see a post claiming you’re eligible for free tokens. To claim them, you must pay a small "gas fee." You send the fee, but no tokens arrive. The scammer keeps the gas fee, and you lose nothing except the small amount you sent. However, some fake airdrops ask you to connect your wallet first, exposing you to the draining risk mentioned above.
Physical and Account Takeovers
Digital security also depends on physical security. SIM-swapping is a tactic where attackers convince your mobile carrier to transfer your phone number to their device. Once they control your number, they can intercept SMS codes used for two-factor authentication (2FA). They then reset your passwords on exchanges and steal your funds. This is why SMS-based 2FA is considered weak for high-value accounts.
Additionally, Crypto ATM scams involve scammers contacting you directly, often claiming you owe a debt or fine. They demand immediate payment via a local Bitcoin ATM. ATMs provide near-anonymous transactions, making recovery impossible. Never send cash to an ATM based on a phone call or message from someone you don’t know personally.
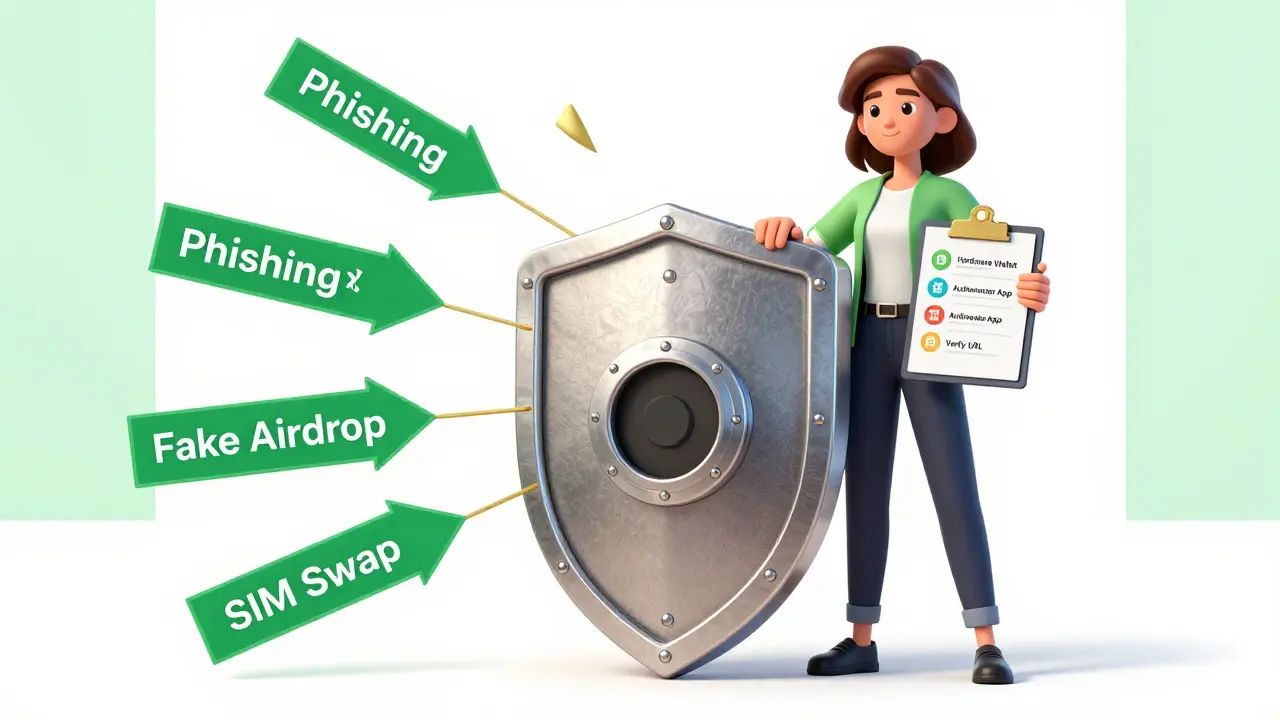
How to Protect Yourself: A Practical Checklist
Prevention isn’t about being paranoid; it’s about being consistent. Here are the non-negotiable steps to keep your assets safe in 2026.
- Use Hardware Wallets: For any significant holdings, move your crypto off exchanges and onto a hardware wallet like Ledger or Trezor. These devices keep your private keys offline, making them immune to most online phishing attempts.
- Verify URLs Manually: Never click links in emails or messages. Type the exchange’s URL manually into your browser or use a bookmarked link. Check for subtle misspellings (e.g., "coinbasee.com").
- Disable Auto-Approvals: Use wallet extensions that allow you to revoke smart contract permissions regularly. Tools like Revoke.cash help you see which apps have access to your funds.
- Upgrade 2FA: Ditch SMS verification. Use an authenticator app (like Google Authenticator or Authy) or a hardware security key (like YubiKey) for multi-factor authentication.
- Treat Private Keys Like Cash: Never share your seed phrase or private key with anyone. No support agent, no website, and no official will ever ask for it.
What to Do If You’ve Been Phished
If you suspect you’ve entered your details on a fake site or approved a malicious contract, act immediately. Time is critical.
- Revoke Permissions: Go to your wallet’s permission manager and revoke all recent approvals.
- Create a New Wallet: Generate a new wallet with a fresh seed phrase. Move any remaining funds from the compromised wallet to the new one immediately.
- Change Passwords: Update passwords for all related exchange accounts, especially if you reused passwords.
- Report It: While you likely won’t recover the funds, reporting the incident to the platform and local authorities helps track scam networks.
The landscape of cryptocurrency is exciting, but it demands vigilance. Scammers are constantly evolving, using AI, social engineering, and technical exploits to bypass defenses. Your best protection is a healthy dose of skepticism and strict adherence to security hygiene. Remember: if it sounds too good to be true, it almost certainly is.
Can I recover my crypto if I fall for a phishing scam?
In most cases, no. Cryptocurrency transactions are irreversible on the blockchain. Once funds are sent to a scammer’s wallet, they cannot be clawed back by exchanges or banks. Prevention is the only reliable defense.
What is the difference between phishing and pharming?
Phishing relies on you clicking a malicious link in an email or message. Pharming redirects you to a fake website automatically, often by compromising DNS servers, so you land on the scam site even if you type the correct URL.
Are hardware wallets completely safe from phishing?
Hardware wallets protect your private keys from online theft, but they don’t protect you from user error. If you are tricked into signing a fraudulent transaction on the device, the funds can still be stolen. Always verify transaction details carefully.
How do pig butchering scams work?
These scams start with a long-term romantic or friendly relationship built online. The scammer gradually introduces a fake investment platform, showing fake profits to build trust. Eventually, they encourage large deposits before disappearing with the money.
Why is SMS two-factor authentication risky?
SMS codes can be intercepted through SIM-swapping attacks, where scammers trick your mobile carrier into transferring your phone number to their device. Using an authenticator app or hardware key is much safer.


